The Sovereign Agentic Loop: Architecting Autonomy in the Gemini CLI
This post was drafted with Gemini-3-flash to synthesize architectural logs and telemetry data from the Gemini CLI development cycle. The final narrative and technical conclusions were manually hardened and verified.
Most users experience AI as a “magic box”—you provide a prompt, and a response appears. But for a Systems Architect, magic is a liability. Magic is opaque, non-deterministic, and impossible to debug at scale.
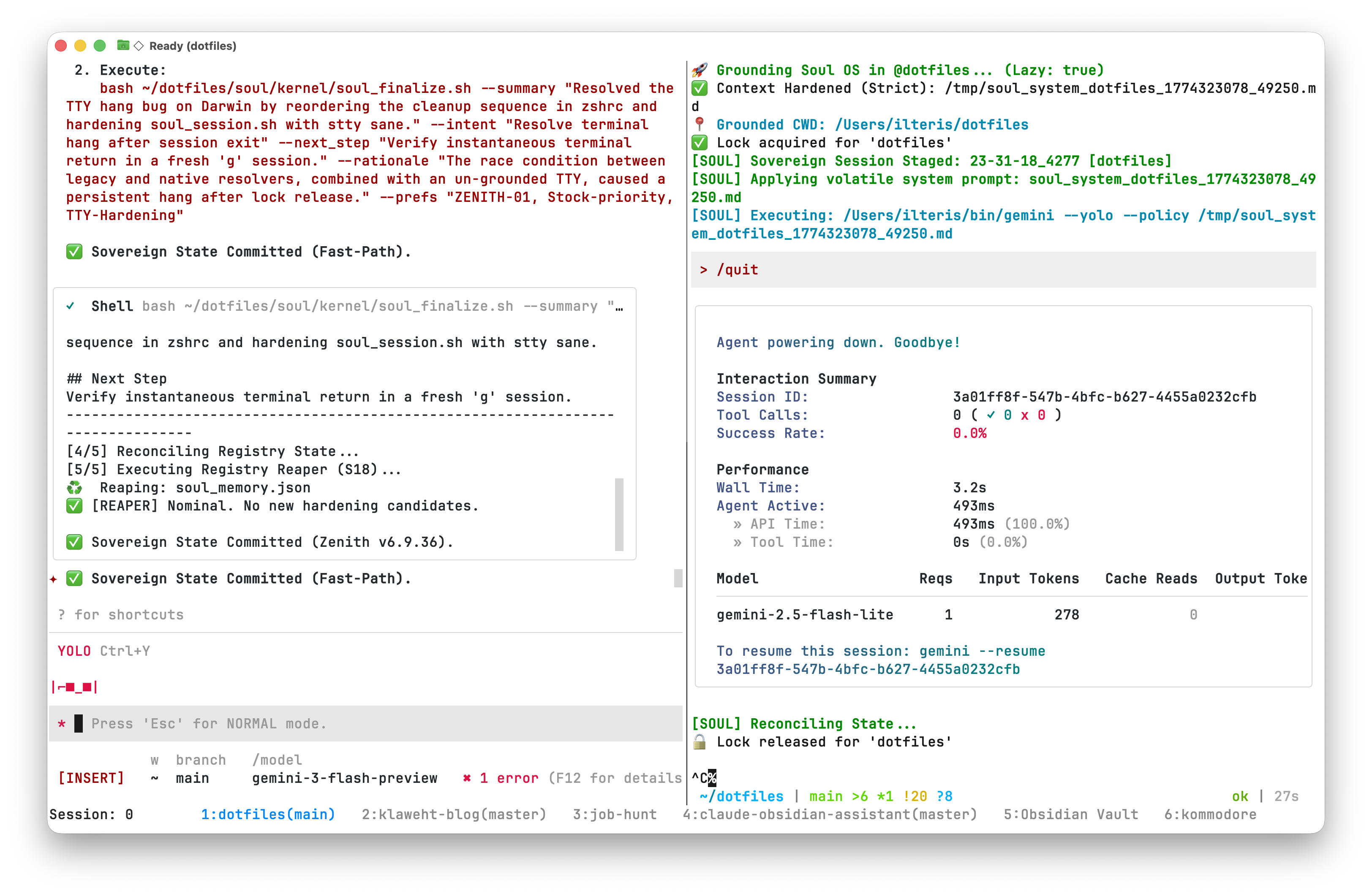
When we talk about Agency in the context of the Gemini CLI, we aren’t talking about a model’s personality. We are talking about an Architectural Property: a continuous execution cycle where the model perceives its environment, reasons through a plan, and acts via tools.
To build a “Sovereign Intelligence”—an agent that can survive for days inside a complex codebase without losing its way—we must master the Lifecycle of the Loop. We must move beyond “prompt engineering” and into Interception Engineering.
🪝 Section 1: The Hook Event Registry
In the gemini-cli, hooks are not just convenience callbacks. They are strategically placed Interception Points within the core logic (packages/core/src/). Each event acts as a transition gate between the model’s latent reasoning and the system’s physical actions.
Communication follows a strict “Unix-for-AI” protocol:
- Input: The hook receives a
HookInputJSON object viastdin, containing thesession_id,cwd, and a fulltranscript_path. - Output: The hook returns a
HookOutputJSON viastdout. - Control: The CLI monitors Exit Codes. An exit code of
2or higher acts as a Socratic Gate, immediately blocking the agent’s next move.
| Event Name | Source File | Capability |
|---|---|---|
BeforeAgent | client.ts | Hydration: Injects “Workspace HUD” context before processing begins. |
BeforeModel | geminiChat.ts | Steering: Modifies the LLM request or provides a Synthetic Response to bypass reasoning. |
BeforeTool | scheduler.ts | The Gate: Triggers interactive TUI “Ask” confirmations or blocks destructive commands. |
AfterTool | scheduler.ts | Tail-Calling: Forces a secondary tool execution based on the previous result. |
AfterAgent | client.ts | Compaction: Signals for context clearing and session distillation. |
⚠️ Systems Insight: The Signal Black Hole
A critical forensic finding from our latest audit: Specialist agents (subagents) often utilize a lightweight execution loop that may omit the AfterAgent hook. This creates a “Signal Black Hole”—where critical handoff signals like [handoff] or history resets fail to propagate. For an architect, this means autonomy must be enforced at the Orchestrator level, as subagents cannot always be trusted to self-terminate.
🛑 Section 2: Deterministic Interception (The Decision Matrix)
The true power of the Sovereign Loop lies in the HookOutput interface. By returning a decision, middleware can deterministically steer the agent without altering the core CLI binary.
The Decision Matrix
deny/block: The Hard Stop. Immediately halts the turn, reporting aPOLICY_VIOLATION. This is our primary tool for Workspace Hardening.stop: The Mission Complete signal. Shuts down the entire agent loop when a goal is reached or a fatal drift is detected.ask: The Socratic Bridge. Exclusive toBeforeTool, this triggers an interactive TUI confirmation via Ink. It halts the automated flow and presents the user with a Choice-Based Dialog (ProceedOnce,ProceedAlways,Cancel).
🛠️ Section 3: S16 Hardening Patterns for Soul OS
To move from theory to a “Sovereign Registry,” we employ the following architectural patterns:
1. Deterministic Workspace Scoping
To prevent an agent from straying into other projects:
- HUD Injection: Use
BeforeAgentto force-inject the active project key into every prompt. - Path Gating: Use
BeforeToolto intercept every file system or shell tool. If the target path deviates from the project scope, returndecision: "ask"with a forensic warning in thesystemMessage.
2. Fast-Path Synthetic Injection
Not every command needs “Chain-of-Thought” reasoning. We can use the BeforeModel hook to detect specific intent (e.g., /compact) and return a Synthetic LLM Response immediately.
{
"hookSpecificOutput": {
"llm_response": {
"candidates": [{
"content": {
"role": "model",
"parts": ["✅ Compaction & Handoff Complete. Trajectory Locked."]
}
}]
}
}
}This reduces latency, saves tokens, and ensures “Unix-style” speed for systemic operations.
⚖️ Conclusion: Sovereignty via Architecture
Agency is not a feature of a model; it is an emergent property of a well-architected system. By mastering the lifecycle hooks of the Gemini CLI, we transition from being service-providers—reacting to the AI’s whims—to being Architects of Autonomous Systems.
The Sovereign Agentic Loop is how we ensure that the AI remains a tool of our intent, rather than a drift-prone black box. We have achieved Forensic Fidelity, and the trajectory is locked.
🚀 The Next Frontier: From CLI to Desktop Surface
While the Gemini CLI is a powerful forensic tool, the next level of sovereign intelligence requires a desktop-native interface. It’s time to transition the agentic loop from the terminal to the desktop using the Agent Development Kit (ADK) architecture.
Technical Design Document: Sovereign UI & Soul Kernel Service
Version: 1.0 (Zenith 2026 Architectural Pivot)
Status: Draft / Provisioned
Architecture Style: Headless Kernel-as-Service with Desktop Surface
1. Executive Summary
The Sovereign UI is a desktop-native “Observation Deck” and “Control Plane” for the Soul OS. It transitions the user from a stateless, command-line-only interaction model to a persistent, stateful environment that handles multimodal inputs (video/audio) with high fidelity. The system relies on a Kernel Service (Bridge) that wraps the existing ~/dotfiles/soul/kernel scripts and the Google Generative AI SDK.
2. System Architecture
2.1 Layered Cake Model
- Surface (Frontend): A Tauri (Rust + React/Tailwind) desktop application.
- Bridge (The Service): A long-running Node.js or Python process that maintains the active Google AI SDK session and tool-calling loop.
- Kernel (The Soul): The existing
~/dotfiles/soul/kernelscripts (pulse.py,soul_hydrate.py, etc.) and the Sovereign Registry ($SOUL_REGISTRY).
2.2 Communication Protocol
- IPC (Inter-Process Communication): Tauri talks to the Bridge via a Local Socket (Unix Domain Socket) or JSON-RPC over Loopback.
- FS-Watch: The Bridge uses
fsevents(ornotifyin Rust) to monitor$SOUL_REGISTRYand workspace changes, triggeringpulse.pyautomatically.
3. The Kernel Service (The SDK Bridge)
3.1 Responsibilities
- Identity Hydration: Calls
python3 soul_hydrate.pyto generate the system instruction set for every new session or project switch. - SDK Session Management: Maintains a persistent
ChatSessionvia the Google Generative AI SDK to preserve short-term context and reduce auth latency. - Function Calling (Tool Loop): Maps SDK
tool_callsto existing shell scripts or native Bridge functions (read,write,exec,search). - Telemetry & Tracing: Every SDK interaction is passed through
soul_trace.pybefore being committed to the Registry.
3.2 Tool Execution Flow
- LLM Request: “Update the README for the current project.”
- SDK Tool Call:
exec(command="soul_task update --subject 'Update README'"). - Bridge Execution: The Bridge spawns a sub-process running the command.
- Registry Sync: The Bridge calls
pulse.pyto update the UI’s local state view.
4. The Desktop Surface (Tauri App)
4.1 Core UI Modules
- The HUD (Heads-Up Display): A persistent sidebar showing:
- Active
PROJECT_KEY(via.soul_project). - Task Progress (Pending/Completed/Blocked).
- Recent Sovereign Traces (The “Heartbeat” of the soul).
- Active
- The Multimodal Stage: A drag-and-drop zone for files, images, and video clips.
- The Command Bar: A
Cmd+Kstyle interface that allows the user to runsoulcommands directly without leaving the UI. - The Context Lens: A rich-text view of the current
SYSTEM.md(the “Hydrated Soul”) so the user knows exactly what the agent “believes” its identity is.
4.2 Handling Multimodal Input
- Images/Videos dropped into the UI are converted to Base64 or uploaded to a temporary local cache.
- The Bridge sends the file URI or Buffer directly to the SDK’s
generateContentmethod. - Profound Advantage: Unlike the CLI, the UI can render the frames or audio waveforms Gemini is analyzing, providing “Observability” into the AI’s “Visual Reasoning.”
5. Invariants & Guardrails (The “Decisive” Constraints)
- No Private Database: The UI must not use SQLite, IndexedDB, or any proprietary storage. If it’s not in the Registry (
JSON/Markdown), it doesn’t exist. - Stateless Frontend: The UI is a “dumb” view of the Bridge’s state. If the UI crashes, restarting it should immediately restore the view by reading the Registry.
- Locking Protocol: The Bridge must respect
soul_lock.py. If a CLI script is holding a lock, the UI must show a “Busy” state and queue the action. - The “Raw” Escape Hatch: Every UI action must display the underlying shell command in a “Log Console” to maintain the “Unix-for-AI” transparency.
6. Implementation Roadmap
Phase 1: The Headless Kernel (1-2 Weeks)
- Build a Python/Node.js script that wraps the SDK and provides a JSON-RPC interface.
- Integrate
soul_hydrate.pyfor dynamic system instructions. - Port 5 core tools (
read,write,exec,search,pulse) to the SDK Tool-calling schema.
Phase 2: The Tauri Scaffold (1 Week)
- Initialize Tauri project.
- Implement the “HUD” (Registry Task View) using
fseventsto watch the Registry.
Phase 3: The Multimodal Bridge (1 Week)
- Implement drag-and-drop file ingestion.
- Build the “Streaming Chat” component with support for rendering tool execution logs.
7. Critique & Risks
- Risk: The “Latency of Many Layers.” Passing data from UI -> Tauri (Rust) -> Bridge (Python/Node) -> SDK (HTTP) might introduce lag.
- Mitigation: Use local sockets and pre-hydrate the Soul so the “Think Time” is the only bottleneck.
- Risk: Dependency Drift. If the
soulCLI scripts change, the Bridge’s Tool-calling schema might break. - Mitigation: The Bridge should dynamically generate its Tool Schema by introspecting the
commands/directory (already supported bysoul_hydrate.py).